SASL
I configured Kerberos on Ubuntu 24.04 WSL and was able to run the following command:
export KRB5_TRACE=/dev/stderr
ldapsearch -H ldap://myserver.my.local -Y GSSAPI
that produced the following output:
SASL/GSSAPI authentication started
[2267891] 1764349156.773981: ccselect module hostname chose cache FILE:/tmp/krb5cc_1000 with client principal administrator@MY.LOCAL for server principal ldap/my.local@LOCAL
[2267891] 1764349156.773982: Getting credentials administrator@MY.LOCAL -> ldap/my.local@ using ccache FILE:/tmp/krb5cc_1000
[2267891] 1764349156.773983: Retrieving administrator@MY.LOCAL -> krb5_ccache_conf_data/start_realm@X-CACHECONF: from FILE:/tmp/krb5cc_1000 with result: -1765328243/Matching credential not found (filename: /tmp/krb5cc_1000)
[2267891] 1764349156.773984: Retrieving administrator@MY.LOCAL -> ldap/my.local@ from FILE:/tmp/krb5cc_1000 with result: -1765328243/Matching credential not found (filename: /tmp/krb5cc_1000)
[2267891] 1764349156.773985: Retrying administrator@MY.LOCAL -> ldap/my.local@MY.LOCAL with result: -1765328243/Matching credential not found (filename: /tmp/krb5cc_1000)
[2267891] 1764349156.773986: Server has referral realm; starting with ldap/my.local@MY.LOCAL
[2267891] 1764349156.773987: Retrieving administrator@MY.LOCAL -> krbtgt/MY.LOCAL@MY.LOCAL from FILE:/tmp/krb5cc_1000 with result: 0/Success
[2267891] 1764349156.773988: Starting with TGT for client realm: administrator@MY.LOCAL -> krbtgt/MY.LOCAL@MY.LOCAL
[2267891] 1764349156.773989: Requesting tickets for ldap/my.local@MY.LOCAL, referrals on
[2267891] 1764349156.773990: Generated subkey for TGS request: aes256-cts/F81B
[2267891] 1764349156.773991: etypes requested in TGS request: aes256-cts, aes128-cts, aes256-sha2, aes128-sha2, des3-cbc-sha1, rc4-hmac, camellia128-cts, camellia256-cts
[2267891] 1764349156.773993: Encoding request body and padata into FAST request
[2267891] 1764349156.773994: Sending request (1658 bytes) to MY.LOCAL
[2267891] 1764349156.773995: Resolving hostname MY.LOCAL
[2267891] 1764349156.773996: Initiating TCP connection to stream 192.168.0.123:88
[2267891] 1764349156.773997: Sending TCP request to stream 192.168.0.123:88
[2267891] 1764349156.773998: Received answer (1679 bytes) from stream 192.168.0.123:88
[2267891] 1764349156.773999: Terminating TCP connection to stream 192.168.0.123:88
[2267891] 1764349156.774000: Sending DNS URI query for _kerberos.MY.LOCAL.
[2267891] 1764349156.774001: No URI records found
[2267891] 1764349156.774002: Sending DNS SRV query for _kerberos-master._udp.MY.LOCAL.
[2267891] 1764349156.774003: Sending DNS SRV query for _kerberos-master._tcp.MY.LOCAL.
[2267891] 1764349156.774004: No SRV records found
[2267891] 1764349156.774005: Response was not from primary KDC
[2267891] 1764349156.774006: Decoding FAST response
[2267891] 1764349156.774007: FAST reply key: aes256-cts/1567
[2267891] 1764349156.774008: TGS reply is for administrator@MY.LOCAL -> ldap/my.local@MY.LOCAL with session key aes256-cts/8ED4
[2267891] 1764349156.774009: TGS request result: 0/Success
[2267891] 1764349156.774010: Received creds for desired service ldap/my.local@MY.LOCAL
[2267891] 1764349156.774011: Storing administrator@MY.LOCAL -> ldap/my.local@ in FILE:/tmp/krb5cc_1000
[2267891] 1764349156.774012: Creating authenticator for administrator@MY.LOCAL -> ldap/my.local@, seqnum 246311139, subkey aes256-cts/7FB1, session key aes256-cts/8ED4
[2267891] 1764349156.774014: Read AP-REP, time 1764349156.774013, subkey aes256-cts/A629, seqnum 1430368257
SASL username: administrator@MY.LOCAL
SASL SSF: 256
SASL data security layer installed.
# extended LDIF
#
# LDAPv3
# base <> (default) with scope subtree
# filter: (objectclass=*)
# requesting: ALL
#
# search result
search: 4
result: 32 No such object
text: 0000208D: NameErr: DSID-0310021C, problem 2001 (NO_OBJECT), data 0, best
match of:
''
# numResponses: 1
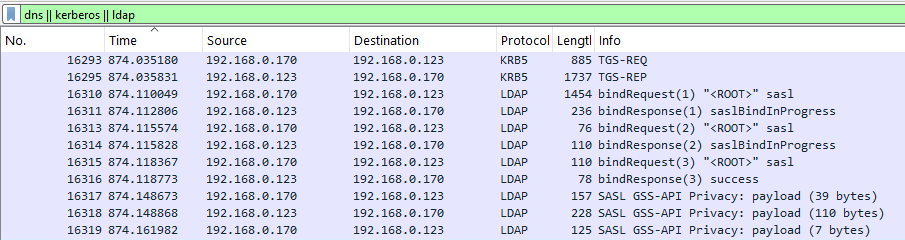
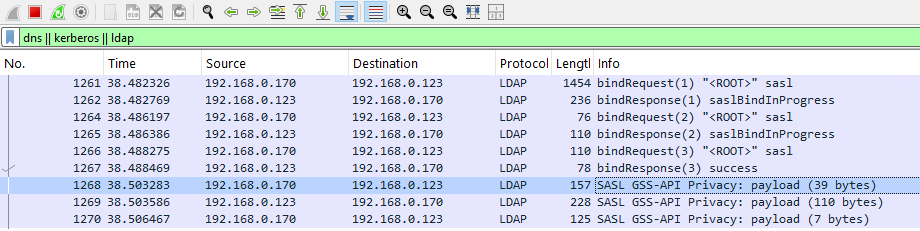
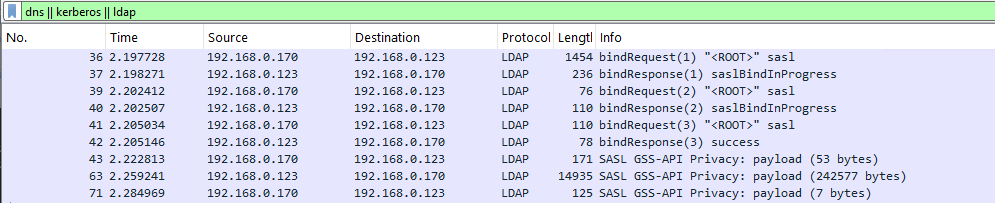
WireShark:
Frame 16310: Packet, 1454 bytes on wire (11632 bits), 1454 bytes captured (11632 bits) on interface \Device\NPF_{D1DF25F0-63A5-4702-A3DA-91F53DB3A5A8}, id 0
Ethernet II, Src: Intel_21:fc:82 (b0:47:e9:21:fc:82), Dst: Microsoft_00:91:01 (00:15:5d:00:91:01)
Internet Protocol Version 4, Src: 192.168.0.170, Dst: 192.168.0.123
Transmission Control Protocol, Src Port: 58604, Dst Port: 389, Seq: 1, Ack: 1, Len: 1400
Lightweight Directory Access Protocol
LDAPMessage bindRequest(1) "<ROOT>" sasl
messageID: 1
protocolOp: bindRequest (0)
bindRequest
version: 3
name: <MISSING>
authentication: sasl (3)
sasl
mechanism: GSSAPI
credentials […]: 6082055406092a864886f71201020201006e8205433082053fa003020105a10302010ea20703050020000000a38204526182044e3082044aa003020105a10a1b084d592e4c4f43414ca21b3019a003020103a11230101b046c6461701b086d792e6c6f63616ca382041830820414
GSS-API Generic Security Service Application Program Interface
OID: 1.2.840.113554.1.2.2 (KRB5 - Kerberos 5)
krb5_blob […]: 01006e8205433082053fa003020105a10302010ea20703050020000000a38204526182044e3082044aa003020105a10a1b084d592e4c4f43414ca21b3019a003020103a11230101b046c6461701b086d792e6c6f63616ca382041830820414a003020112a103020105a28204060482
krb5_tok_id: KRB5_AP_REQ (0x0001)
Kerberos
ap-req
pvno: 5
msg-type: krb-ap-req (14)
Padding: 0
ap-options: 20000000
ticket
authenticator
[Response In: 16311]
Frame 16317: Packet, 157 bytes on wire (1256 bits), 157 bytes captured (1256 bits) on interface \Device\NPF_{D1DF25F0-63A5-4702-A3DA-91F53DB3A5A8}, id 0
Ethernet II, Src: Intel_21:fc:82 (b0:47:e9:21:fc:82), Dst: Microsoft_00:91:01 (00:15:5d:00:91:01)
Internet Protocol Version 4, Src: 192.168.0.170, Dst: 192.168.0.123
Transmission Control Protocol, Src Port: 58604, Dst Port: 389, Seq: 1479, Ack: 263, Len: 103
Lightweight Directory Access Protocol
SASL Buffer Length: 99
SASL Buffer
GSS-API Generic Security Service Application Program Interface
krb5_blob: 050406ff00000000000000000eae68e49ec405ad7e1d437c9acf8e44a12e24912c119972068d4b80b0ec08fb82195b24fcf0a66c83090ca3c2bc72cb
krb5_tok_id: KRB_TOKEN_CFX_WRAP (0x0405)
krb5_cfx_flags: 0x06, AcceptorSubkey, Sealed
krb5_filler: ff
krb5_cfx_ec: 0
krb5_cfx_rrc: 0
krb5_cfx_seq: 246311140
krb5_sgn_cksum: 9ec405ad7e1d437c9acf8e44a12e24912c119972068d4b80b0ec08fb82195b24fcf0a66c83090ca3c2bc72cb
GSS-API Encrypted payload: 97236928db32558d49dc697a480b0d319e1a6ca863e7bab805491868da51408acf4ea9798b93d5
ldapsearch -H ldap://myserver.my.local -Y GSSAPI -o sasl_secprops=none
SASL/GSSAPI authentication started
[2272880] 1764349964.859162: ccselect module hostname chose cache FILE:/tmp/krb5cc_1000 with client principal administrator@MY.LOCAL for server principal ldap/my.local@LOCAL
[2272880] 1764349964.859163: Getting credentials administrator@MY.LOCAL -> ldap/my.local@ using ccache FILE:/tmp/krb5cc_1000
[2272880] 1764349964.859164: Retrieving administrator@MY.LOCAL -> krb5_ccache_conf_data/start_realm@X-CACHECONF: from FILE:/tmp/krb5cc_1000 with result: -1765328243/Matching credential not found (filename: /tmp/krb5cc_1000)
[2272880] 1764349964.859165: Retrieving administrator@MY.LOCAL -> ldap/my.local@ from FILE:/tmp/krb5cc_1000 with result: 0/Success
[2272880] 1764349964.859166: Creating authenticator for administrator@MY.LOCAL -> ldap/my.local@, seqnum 770609695, subkey aes256-cts/1700, session key aes256-cts/8ED4
[2272880] 1764349964.859168: Read AP-REP, time 1764349964.859167, subkey aes256-cts/9CA1, seqnum 938398489
SASL username: administrator@MY.LOCAL
SASL SSF: 256
SASL data security layer installed.
# extended LDIF
#
# LDAPv3
# base <> (default) with scope subtree
# filter: (objectclass=*)
# requesting: ALL
#
# search result
search: 4
result: 32 No such object
text: 0000208D: NameErr: DSID-0310021C, problem 2001 (NO_OBJECT), data 0, best
match of:
''
# numResponses: 1
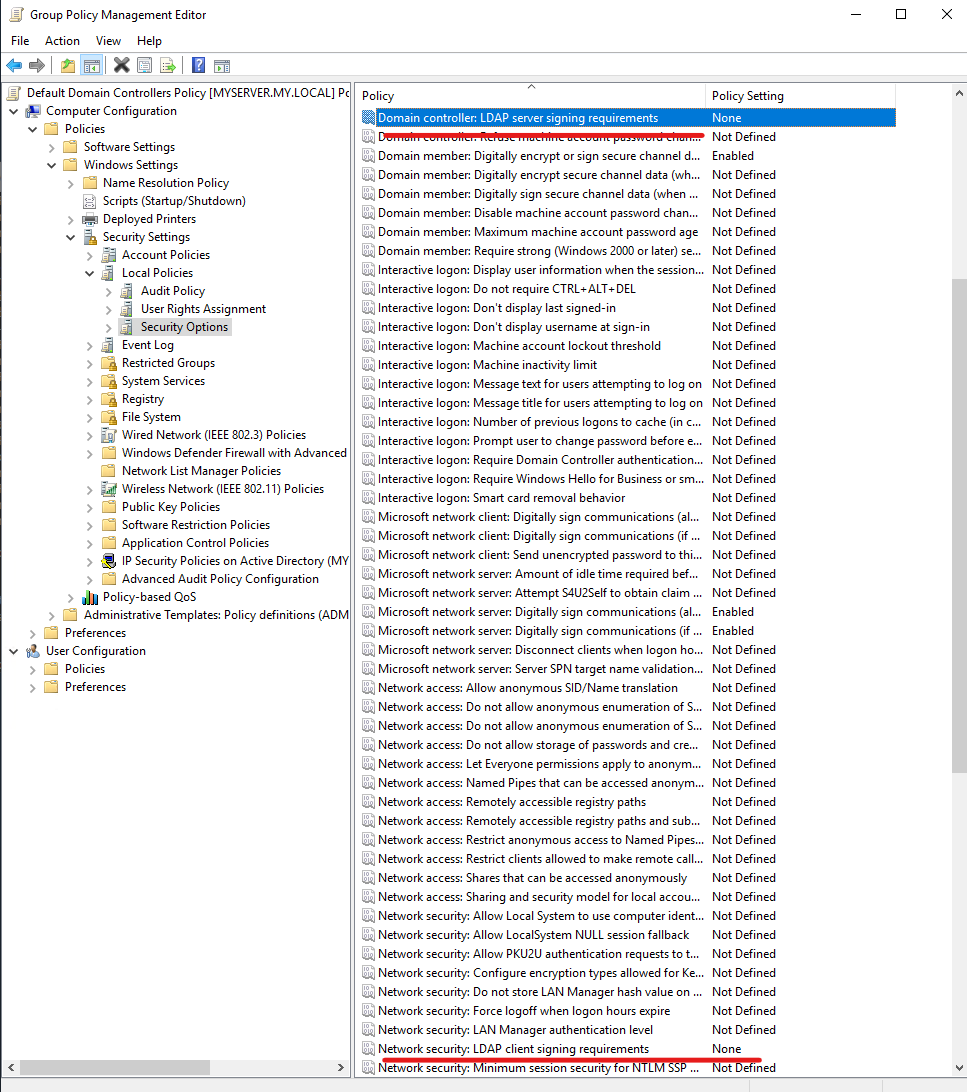
I set the both options to none:
and tried
ldapsearch -H ldap://myserver.my.local -Y GSSAPI -o sasl_secprops=none
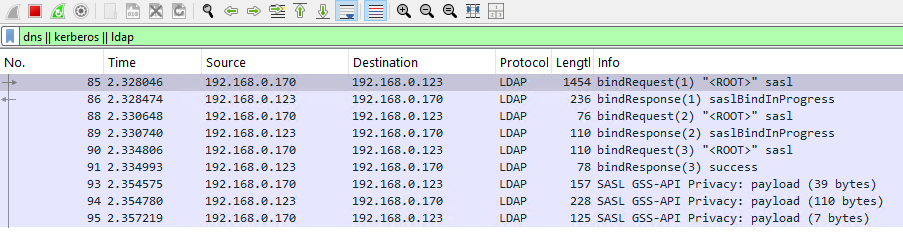
again, but there still were SASL GSSAPI Privacy in WireShark:
ldapsearch -H ldap://myserver.my.local -Y GSSAPI -o sasl_secprops=none -b "DC=my,DC=local"
Simple Bind
ldapsearch -H ldap://192.168.0.123 389 -x -D $ad_user -w $ad_password -b "DC=my,DC=local"
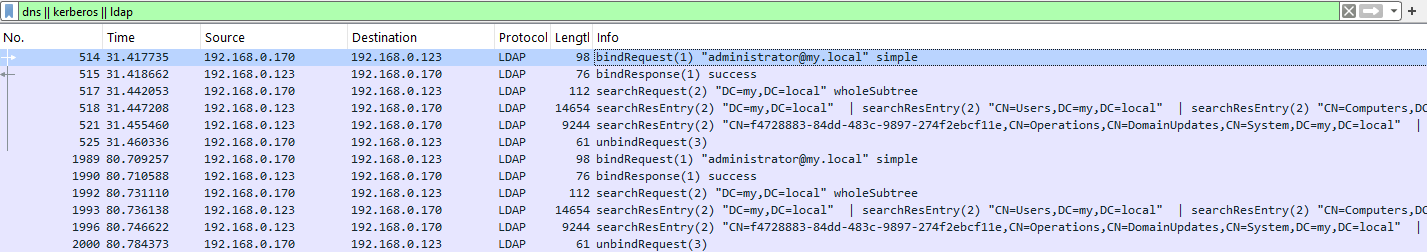
Frame 514: Packet, 98 bytes on wire (784 bits), 98 bytes captured (784 bits) on interface \Device\NPF_{D1DF25F0-63A5-4702-A3DA-91F53DB3A5A8}, id 0
Ethernet II, Src: Intel_21:fc:82 (b0:47:e9:21:fc:82), Dst: Microsoft_00:91:01 (00:15:5d:00:91:01)
Internet Protocol Version 4, Src: 192.168.0.170, Dst: 192.168.0.123
Transmission Control Protocol, Src Port: 58650, Dst Port: 389, Seq: 1, Ack: 1, Len: 44
Lightweight Directory Access Protocol
LDAPMessage bindRequest(1) "administrator@my.local" simple
messageID: 1
protocolOp: bindRequest (0)
bindRequest
version: 3
name: administrator@my.local
authentication: simple (0)
simple: 1234@abc